Security is extremely important to us here at Oracle, in fact, maybe it’s the #1 priority as we want to protect your data and by extension, YOU.
So one of our 3rd party libraries had a Cybersecurity Vulnerability pop-up, which necessitated an update for SQLcl.
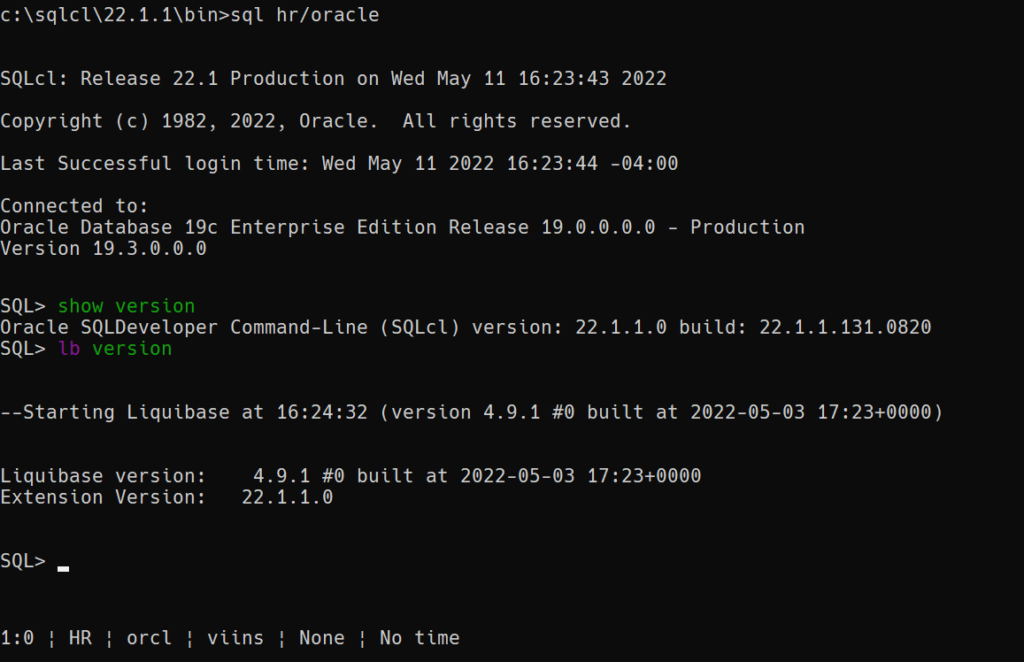
We’ve updated our Liquibase extension up to version 4.9.1.
And while we were at it, we fixed a few bugs as well – 8 of them for our enhanced Liquibase support in SQLcl!
| 34049379 | ON STARTUP GET WARNING ABOUT WINDOWS REGISTRY KEY NOT FOUND |
| 34141455 | SQLCOMPLETER NO VALIDATION ON POSITION VALUE |
| 34088656 | ISSUES WITH LB HELP GENOBJECT AND UNTAG |
| 34062379 | LIQUIBASE INCONSISTENT STATE AFTER PARTIALLY APPLIED CHANGE IN CHANGESET |
| 34048962 | LIQUIBASE HELP NOT WORKING |
| 34040532 | LIQUIBASE SPOOL DOES NOT SAVE THE OUTPUT INTO LOG FILE |
| 34037051 | ABNORMAL BEHAVIOUR OF UPDATE, ROLLBACKSQL, AND ROLLBACK WITH TRIGGER OBJECT TYPE |
You can find SQLcl at the regular places, the Yum repos and OCI will follow shortly as well.
Meanwhile over on the Oracle Cloud (OCI)
SQLcl in Cloud Shell still remains version 21.4, it’ll be upgraded shortly. When it does, you’ll have to tell OCI that you want to use Java 11 vs 8. 11 is our new minimum version of Java supported for all 22.x releases in Database Tools Land (SQLDev, SQLcl, ORDS…)
To do this –
csruntimectl java listYou’ll get a list of Java Homes available, most likely an 8 (the current default) and an 11.
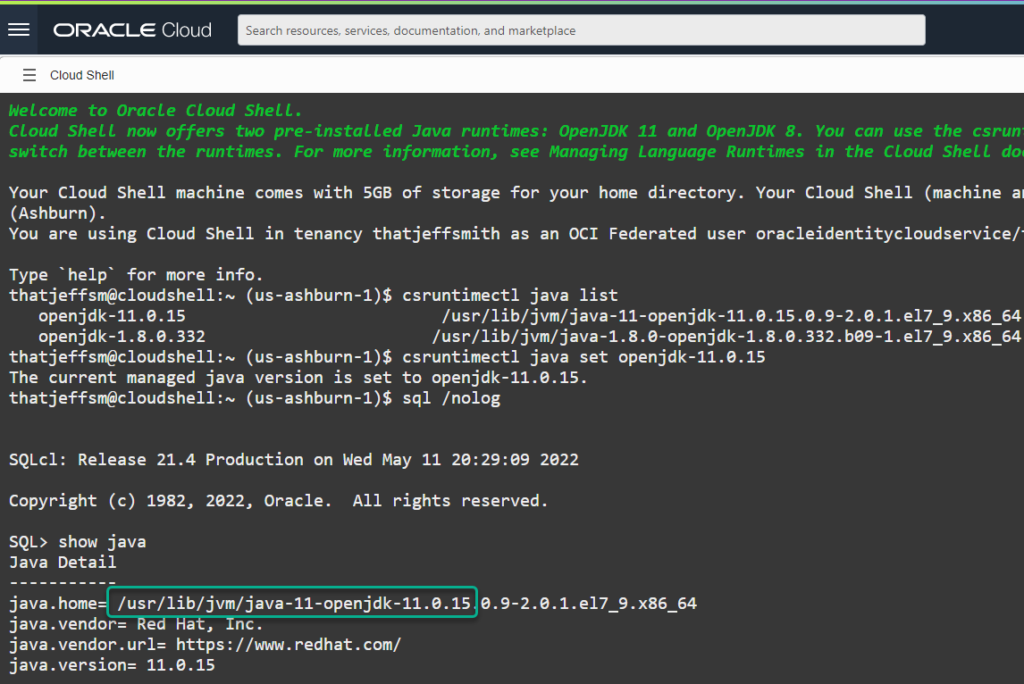
By following the docs, I can see the proper command to change the home remains csruntimectl.
csruntimectl java set openjdk-11.0.15Now we’re all good and set to go.
Speaking of OCI…Console Updates
A few of us noticed a couple of changes today:
- Dialog to optionally choose some IT roles you fill, to help shape the console offerings
- Service Links on the Get Started Page
What I select in the list of profiles will directly influence what I see in the RECOMMENDED box.
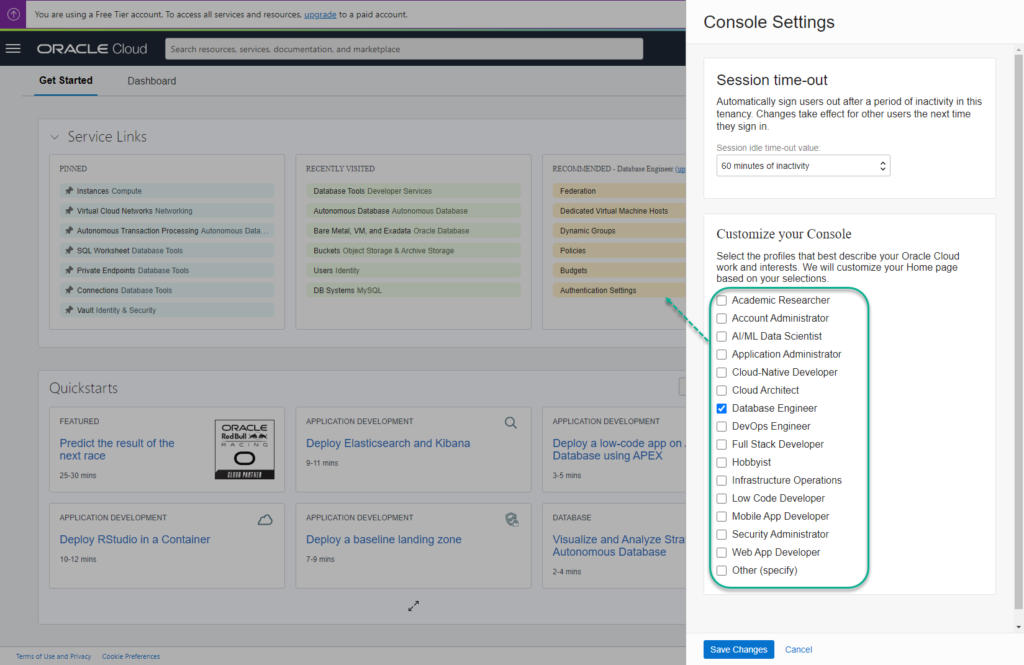
I can of course change that by going into Console Settings…
Or just using the home page shortcuts, things I’ve used recently before…and yeah, let’s also show off the SSO access to your Autonomous Database via the ADMIN account.





2 Comments
Have been waiting for Service Links! So tired of clicking so much! Thanks!
OCI Console? I’ve been quite fond of the ‘bookmarks’ you can permanently pin in your mega menu…